
Secure Network Storage
All communications encrypted by nature. Session information protected with JSON web tokens and limited Time to Live.
Designed by cybersecurity experts to protect your data and respect the confidentiality of your communications
Complete privacy with E2E encryption. All communications use AES-256 for real-time calls and RSA-2048 for file sharing. Peer-to-Peer architecture ensures internal communications remain local and perfectly secure

All communications encrypted by nature. Session information protected with JSON web tokens and limited Time to Live.

No data stored on your devices except JWT tokens. All loaded data is immediately destroyed when you close the application.
Designed to defend your infrastructure against evolving attack vectors
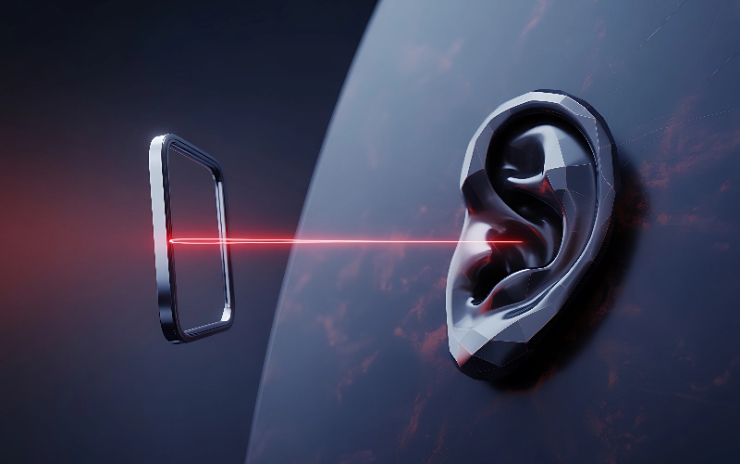
Advanced encryption prevents unauthorized listening to your communications. Every call and message is protected from interception.

Multi-layer security architecture and root device prevention block unauthorized access attempts and protects against data theft.

European server deployment or SaaS mode protects you from foreign data access laws and regulations.
Your data and communications belong only to you, and Private Discuss respects your privacy by encrypting everything in transit.
Shield your team’s most sensitive discussions with a workspace designed to prevent interception and data leakage.
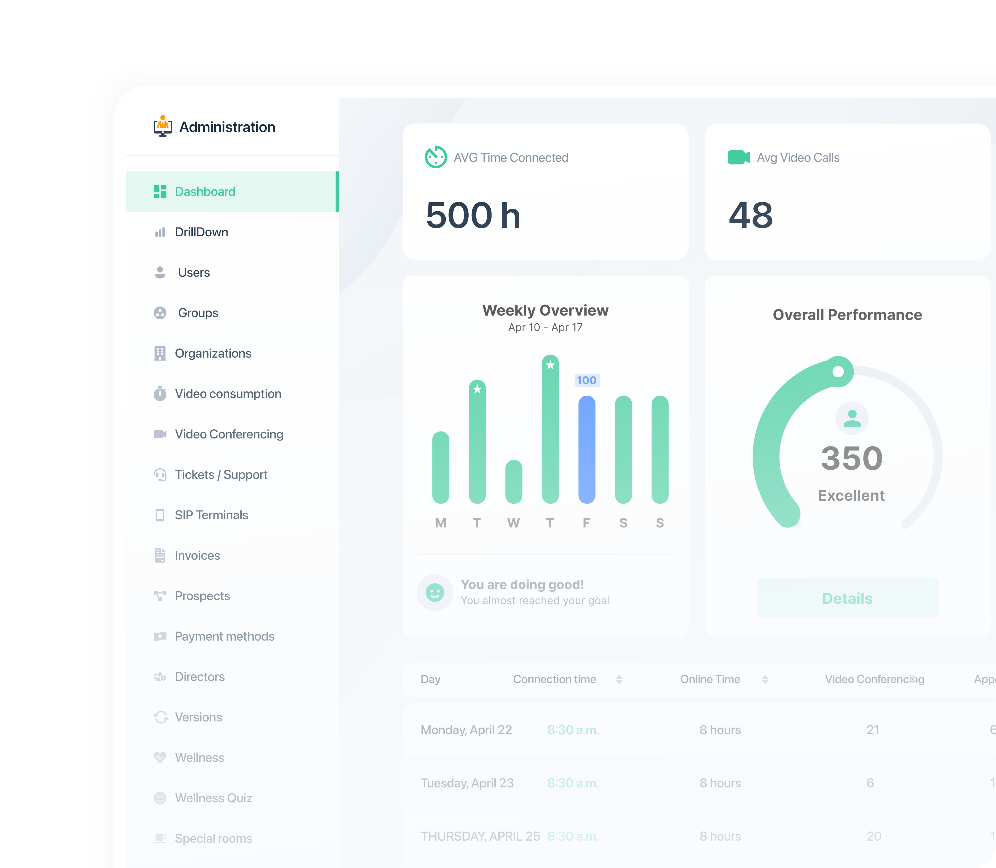
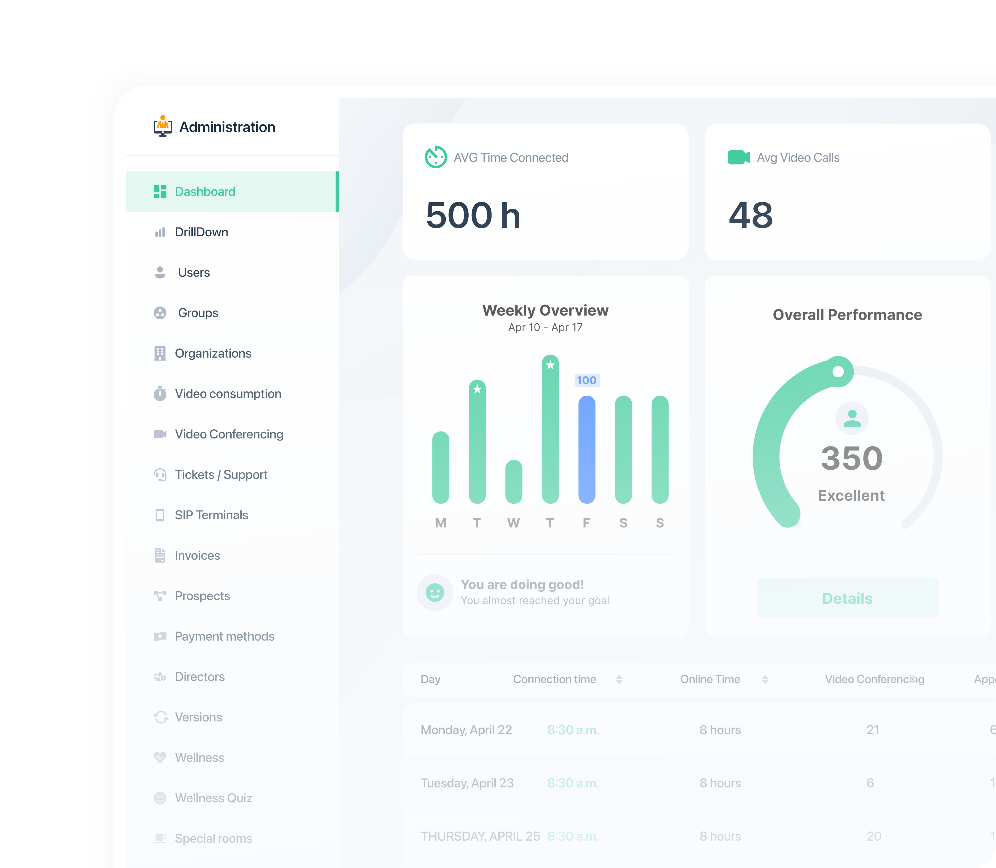
Empower your security teams with absolute oversight of the environment without compromising user privacy.
We treat your privacy as a mission-critical asset, ensuring zero third-party access to your organization's data.
Join the world’s leading organizations in reclaiming data sovereignty. Request a private consultation with our security architects to tailor a solution for your enterprise.
Contact Us